Technical
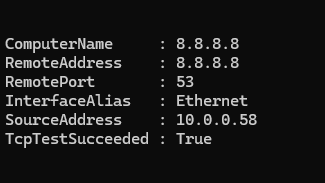
From a Windows powershell terminal in the above just change name/ip-here to the name or ip of what you are testing then change port-number-here to the port number you need to check. Test-NetConnection -ComputerName 8.8.8.8 -Port 53 The above example is checking if TCP/IP port 53 (DNS) is open on […]
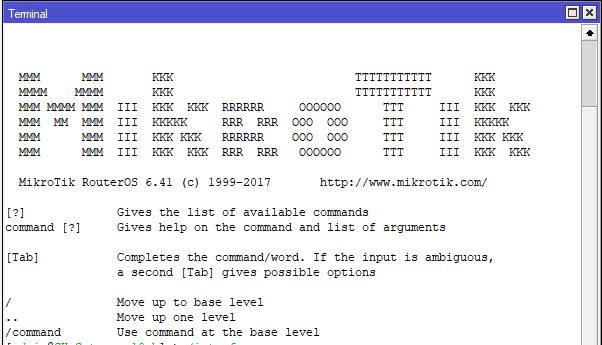
This is a simple and crude method to disable an interface based on the volume of data that has gone through it. In the below example we will be using the rx bytes on ether4 In the example above the above script is scheduled to run every 5 mins, if […]
Below is a simple example of how to use QOS for VOIP in ROS /ip firewall mangleadd action=mark-connection chain=prerouting comment=\“Mark Voip Connections SRC” new-connection-mark=voip_connections \passthrough=yes src-address-list=voipadd action=mark-connection chain=prerouting comment=\“Mark Voip Connections DST” dst-address-list=voip new-connection-mark=\voip_connections passthrough=yesadd action=mark-packet chain=prerouting comment=”Mark Voip Packets SRC” \connection-mark=voip_connections new-packet-mark=voip_packets \passthrough=no src-address-list=voipadd action=mark-packet chain=prerouting comment=”Mark Voip Packets […]
This adjusts the number of days to keep quarantined email etc/MailScanner/defaults /var/www/mailscanner/conf.php days to keep need to be edited in both the above files
These are the domains to harvest IP addresses for; .facebook.com.fbcdn.net.facebook.net Add your local src IP Subnet to the rule below, then repeat twice more using .fbcdn.net and .facebook.net chain=forward action=add-dst-to-address-list src-address=YourLocalIpSubnet address-list=Facebook IPs address-list-timeout=4d content=.facebook.comlog=no log-prefix=”” Next add the rule below, this rule will block any IP on your local […]
The best way is to create a new firewalld zone and we add the specific IP to that zone. To start with lets create an appropriate zone, in this example we will call the zone webmin-access and open webmin to 1 specific IP address. The port will be 10000 tcp […]
nmap -sT targetIP/hostname nmap –script vuln targetIP/hostname -O trys to identify Operating System, example nmap -sT -O targetIP/hostnam